Wow, this is pretty massive. The Irish Payment Services Organisation has again released details of a credit-card breach, this time on retail Point-of-Sale card terminals. Quoting the Irish Examiner story:
Una Dillon, head of card services at the Irish Payment Services Organisation, said the criminals went into the shops pretending to be doing maintenance work on behalf of the banks.
“We have discovered only in the last 48 hours that a number of retailers have been affected by a point-of-sale compromise,” she said. “We are in the lucky position that it was discovered quickly and the gardaí are working on it.
“Gardaí have uncovered a lot of the devices and CCTV footage. We have a list of all the card numbers that have been used. They have either been blocked or restrictions put on those cards.
“With the devices recovered it may just be that the cards were only saved and the criminals did not have a chance to get hold of the card numbers.”
“There will be an emergency meeting today with the gardaí, the terminal vendors and the banks to try and close down on this,” she said, adding the gardaí were in pursuit of the gang.
Insufficient authentication of maintainance staff is being blamed:
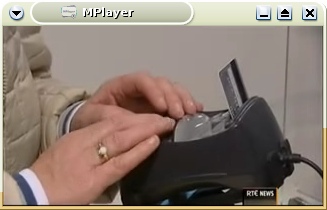
“The criminals have been going into shops claiming to be engineers working on the terminals. Staff are used to their bank officials coming to update terminals so unfortunately they have been able to do that.
Bank of Ireland estimated 3,100 of its debit and credit cards were affected and Ms Dillon said the other eight card providers could have similar numbers.
Bank of Ireland said, as a temporary measure, it had reduced the daily withdrawal limit on all its debit cards for ATM transactions outside Ireland to just €100 to protect customers from fraud.
They haven’t released the names of the affected shops yet; 20,000 cards, though, sounds like it’s been going on for while, on a large scale. Yikes.
The SiliconRepublic story claims that the gang ‘plugged in wireless devices that pushed the data to the internet and allowed the card numbers to be used overseas.’ However, in the past, these ‘wireless devices’ didn’t use the internet; instead they use parts from mobile phones, which relayed PINs, card numbers and CVV security codes via SMS text messages to Romania. That model seems more likely here, I would guess, due to the reliability of phone networks.
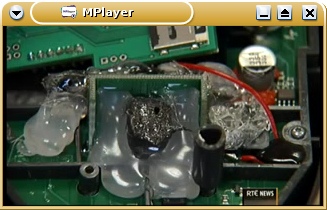
Update: last night’s RTE Six-One news bulletin (viewable as streaming RealVideo or transcoded 5MB AVI file), made it clear that the hardware used phone components and SMS. It had some pretty good pics of what appears to be a sample subverted POS terminal:



VISA have been warning about attacks on petrol-pump-based POS terminals since 2006, e.g. this story, but they’re more easy to attack since there’s few or no staff present by the pumps when the POS terminal subversion takes place. This has resulted in most petrol stations in Ireland disabling POS credit-card payment systems, requiring customers to pay at the counter; we lose convenience, but at least we’re probably not being skimmed. But these in-store POS terminals seem to be increasingly under attack; there are reports from Livigno, Italy, Rhode Island, and Canada.
The tamper-proofing of POS terminal hardware is unreliable; it’d be nice to see them made harder to tamper with. I would guess the gang used secondhand, hacked POS terminals, which supposedly should be tamper-evident (ie. easy to spot modifications).
Better yet, if Chip-and-PIN cards used end-to-end crypto between a crypto smartcard and the bank’s central systems, POS hacks would be impossible. But there’s no sign of that happening.
Most importantly, IPSO has promised that ‘banks will refund any customers whose details have been used to make fraudulent transactions.’ That’s key. It’s interesting to note that IPSO have been hammering home this point repeatedly in their stories — they’re worried about customer confidence, I’d guess.
Comments closed